
¶ What is FlowSpec?
FlowSpec, or Flow Specification, refers to an approach in configuring network traffic policies. It allows for a more granular and precise definition of routing rules and flow control, enabling dynamic adaptation to different types of DDoS attacks targeting our networks.
¶ What is the purpose of a template FlowSpec?
The template of FlowSpec is a predefined framework that simplifies the process of creating and implementing FlowSpec rules. It serves as a standardized template, providing a consistent foundation for specific network traffic policy configurations. This template may include parameters such as source addresses, destination addresses, protocol, ports, and other relevant characteristics.
As DDoS attacks change, FlowSpec templates provide flexibility to make dynamic adjustments to network traffic policies. This allows for a responsive reaction to changes in network conditions, ensuring efficient adaptation to this constant evolution.
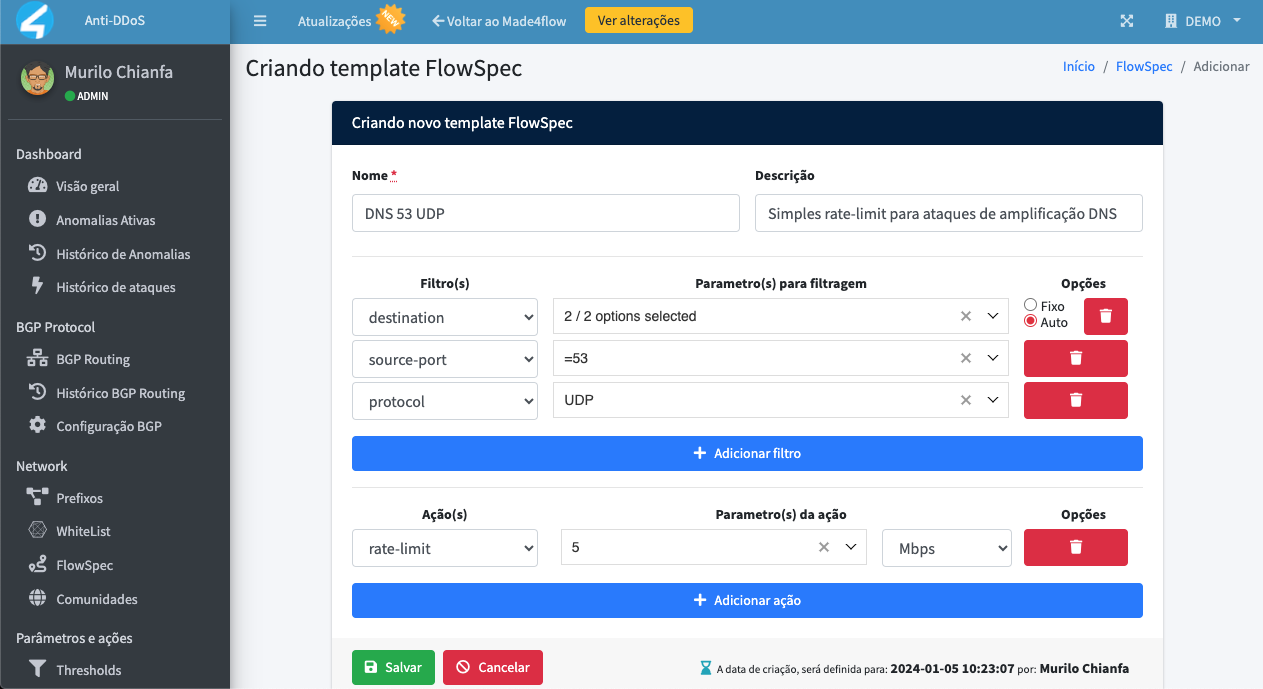
¶ Creating a FlowSpec template
To start, let's create a FlowSpec rule to protect us against DNS amplification attacks, which pose a significant threat by exploiting vulnerabilities in the DNS protocol to flood targets with excessive traffic.
Unlike RTBH advertisements, in FlowSpec we have the option to use proactive rate-limiting measures, aiming not to completely cut off network traffic, but rather to let some bits pass through to try to provide a better perception to the target of the attack than simply cutting it off from the internet.
To specifically mitigate these types of attacks that typically involve sending many packets with a source port of 53 using the UDP protocol, we will develop a FlowSpec rule that directly addresses these characteristics, adding a rate limit slightly above the usual for day-to-day operations:
¶ Possible actions
¶ Adding FlowSpec templates to responses
Now that we have the FlowSpec template, let's create some automatic actions and responses for new anomalies detected with this signature: